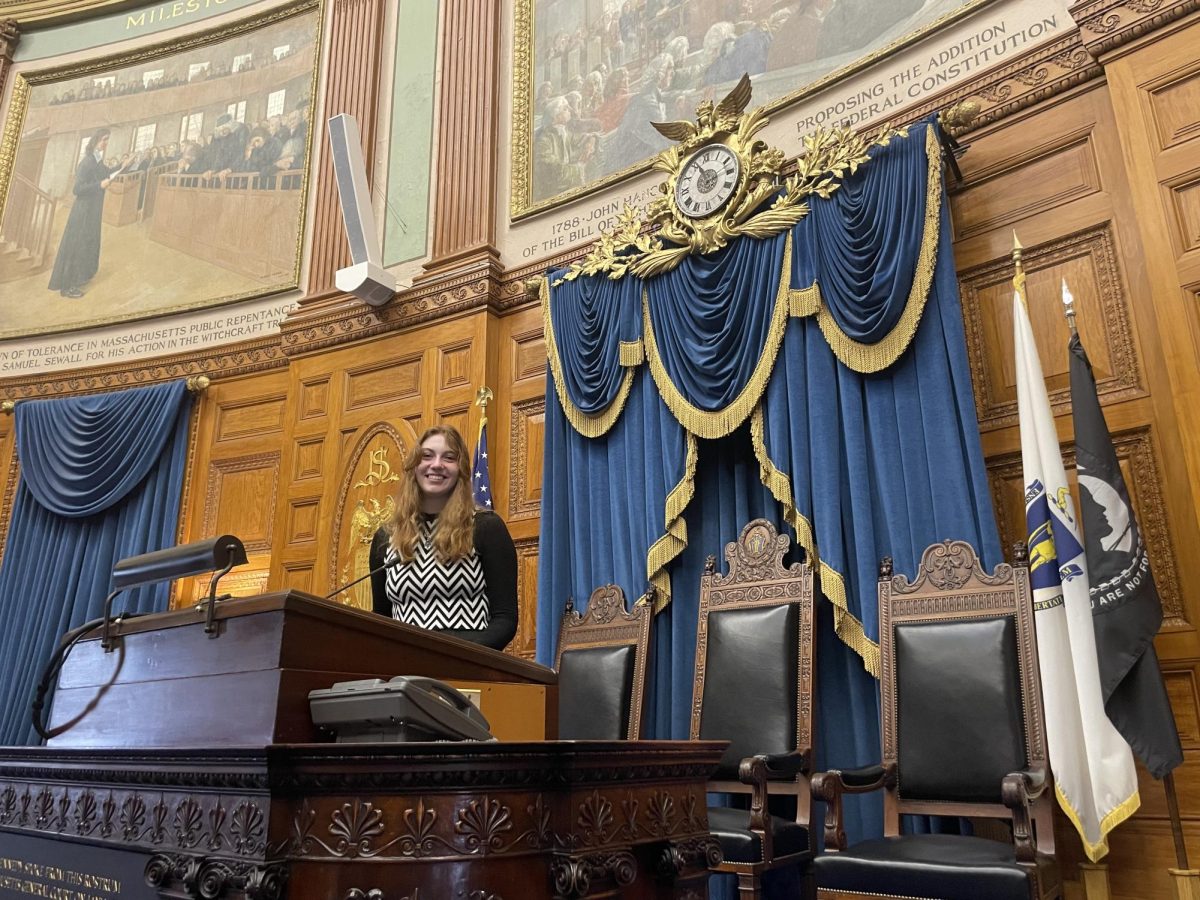
Two professionals took on the question of what is next in cyber security during Thursday’s Ford Hall Forum, “Balancing Cyber Security with Privacy in the Digital Age.” Sqrrl Enterprise Business Manager Ely Kahn and Northeastern University Visiting Fellow Ryan Maness led the discussion on how far is too far in protecting cyberspace.
The initiative for the forum, WorldBoston, has held a variety of international events for almost 100 years, and is now covering the issue of cyber security at a time when the Internet is a dominant aspect of everyday life.
Kahn, who has background with national security within the White House, made it clear that he has experience with cyber security as well. Sqrrl is “a security intelligence platform that enables organizations to target, hunt, and disrupt advanced cyber threats,” according to their website.
Kahn explained a network of pipes that link cyberspace together and can be attacked. The main points of attack against cyber security, according to Kahn, are split into four categories: criminal, hacktivist, espionage, and war.
“Cyberspace is a very physical infrastructure,” he said.
Attacks on cyberspace, according to Kahn, are taken seriously due to the fact that main security organizations in the United States, including the FBI, CIA, NSA, and the military, use cyberspace. These attacks come not only from hackers in the U.S., but from other countries searching for information, like China.
“The term ‘cyberwar’ drives me crazy,” said Kahn, referring to the conflicts happening in cyberspace. He went on to say that it is not a war, but rather incidents that are taken care of by the major security organizations.
“The types of attacks that are being perpetrated, or at least the weapons and tools that are available to hackers, has certainly been growing,” he said.
Kahn presented three cyber security policies that he believes need to be implemented in order to increase the protection of secure information.
The first policy involves information-sharing. The U.S. is attempting to pass a proposed law, the Cyber Intelligence Sharing and Protection Act, that would allow the government to have access to information from major companies and organizations, which would then help the U.S. prevent cyber attacks.
According to Kahn, the act, although it would allow major security organizations to gather information from mainstream companies, would protect the U.S. from major cyber attacks.
Preventing espionage, explained as a main point of cyber attacks, was Kahn’s second policy. He said he believes illegal spying can be prevented by the first policy within CISPA. The U.S. does not want other countries or enemies spying on them, so preventing such actions is a major aspect of enhancing cyber security.
This leads into the third policy of balancing offense versus defense. In this case, Kahn explained the “disclosure of information versus the use of the information against enemies.” To Kahn, major security organizations need to be careful of the information they have and how they use it.
To further Kahn’s claims and policies, Maness introduced “The Era of Cyberpeace?” Maness described that the idea of “cyberpeace” says that there is no violence in the cyber world, but there is still conflict, which is defined as negative peace.
Ultimately, the goal is to obtain positive peace, or no conflict.
Kahn said that cyber espionage is on the rise, and creating awareness among the general public will make it preventable.